Secure document shredding specialists deal with physical and digital data on a regular bases. How we handle this data is important to ensure confidentially. Confidential shredding and data protection go hand in hand to prevent data breaches occurring.
It is widely known that employees and hackers are biggest cause of data breaches. There have being high profile hacking cases involving employees inappropriately clicking on links that permits the hackers access to the organisations network and software system.
In order to have an appropriate confidential document and data disposal system in place, you should firstly contact a service provider whom has ample experience in the industry with a 100% clean track record (i.e. an occurrence of zero data breaches). Such a Data Service Provider will be able to answer all your queries and concerns regarding how to implement a secure and efficient document management system – all the way to end of life documents as well as in-house training of staff and policies and procedures. “At the end of the day, you are relying on employees to manage confidential documents in a secure and confidential manner.”

In order for one to have piece of mind, a training programme should be established for the induction and on-going training (in-house) for the organisations employees. When the employees understand the importance of efficient and accurate Data Management and Data Protection Legislation; it minimises the risk of a data breach.
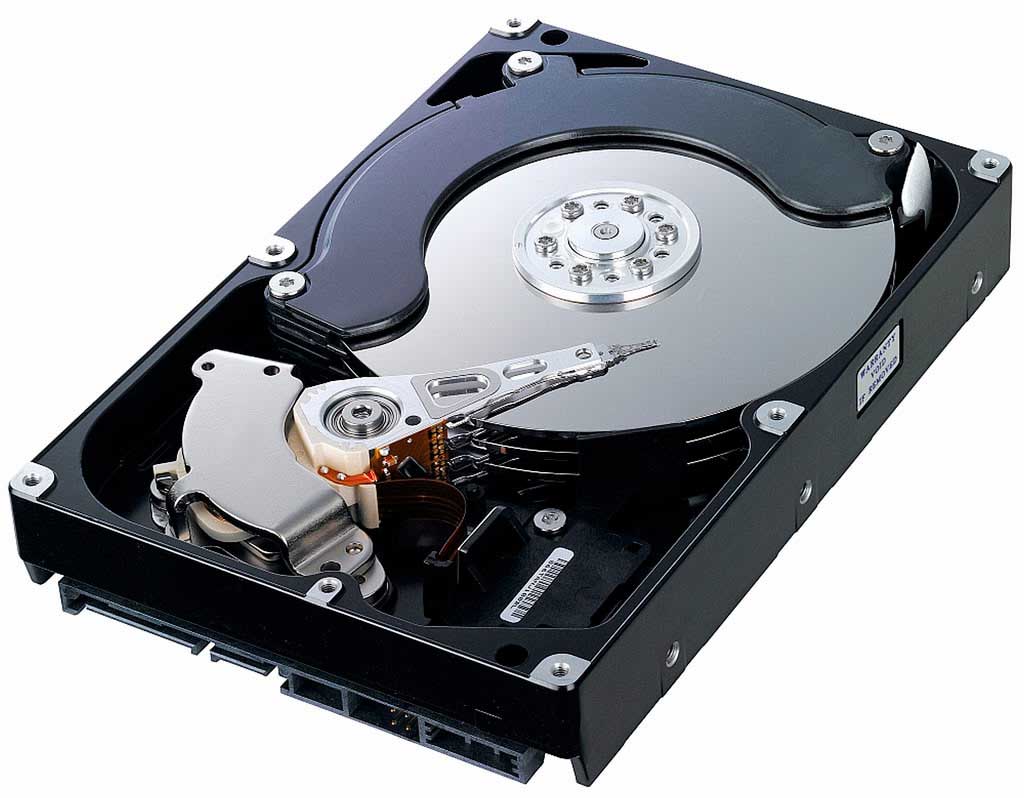
When the data reaches its end of life, it needs to be securely disposed of. This is where a certified professional Data Processor like Security in Shredding provides (at the clients choice) onsite and/or offsite data destruction. A company such as Security in Shredding are specialists in the entire area of Data Management. They have an unblemished record and provide a professional, certified and recognised data destruction services.
In order for an organisation to maximise compliance in the workplace, proper appropriate disposal of information has to be made easily accessible for the employee.
Security in Shredding do not recommend placing a recycling bin in close proximity to a printer of copying machine for example as employees can easily discard the unwanted copies or data into the recycling bin. However, Security in Shredding can implement secure lockable consoles throughout the building in specific locations as requested by the organisation and also in close proximity to the copying or printer machines.
If you wish to have a conversation with any of our Data Consultant Specialists, you can pick up the phone and dial +67 24848 or email us at info@securityinshredding.com.
Specialising in secure confidential document shredding services with a reputation for exceptional security, customer service. Delivering value for money and the utilisation of leading technology compliant to the highest security standards within the industry.